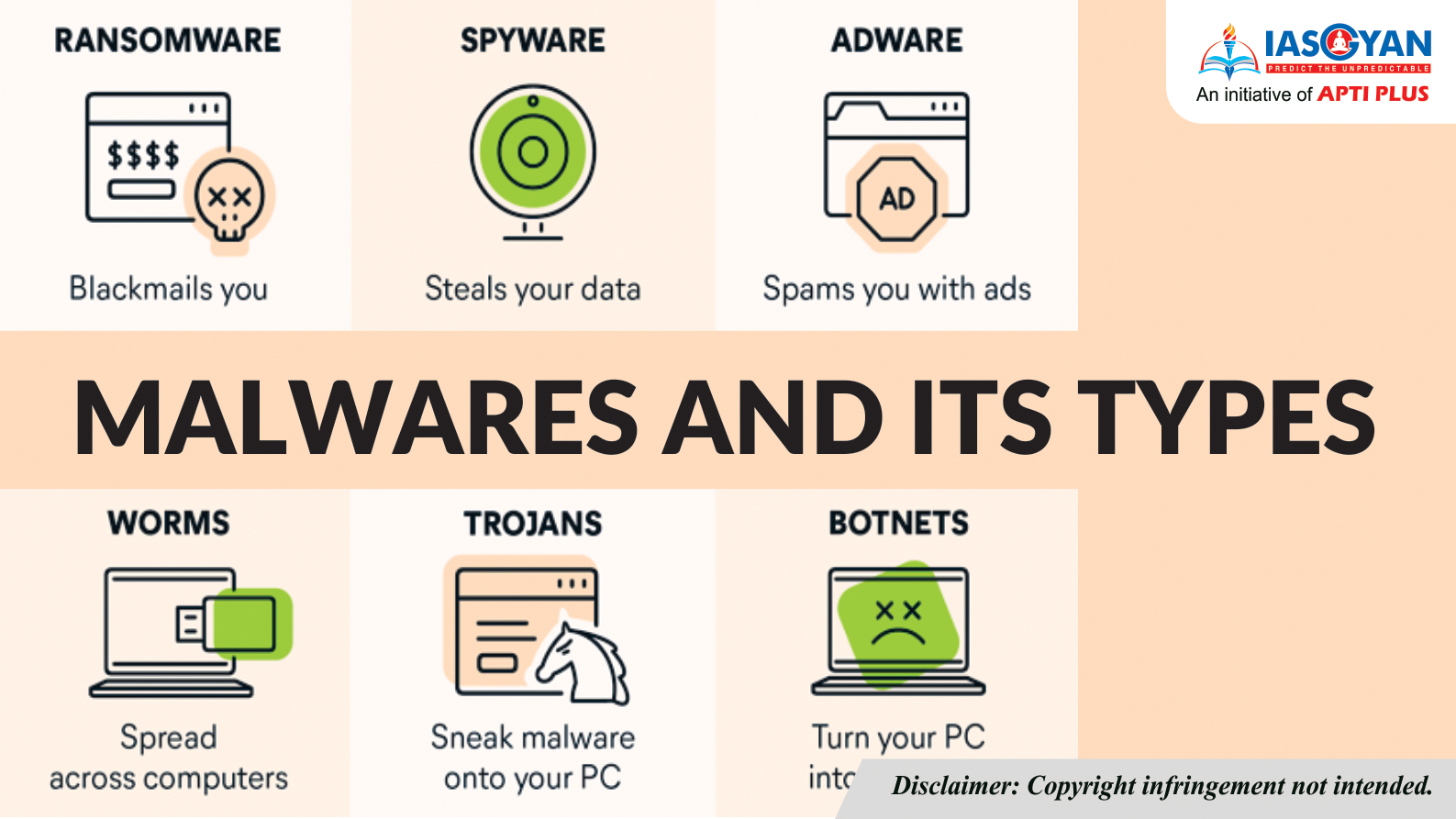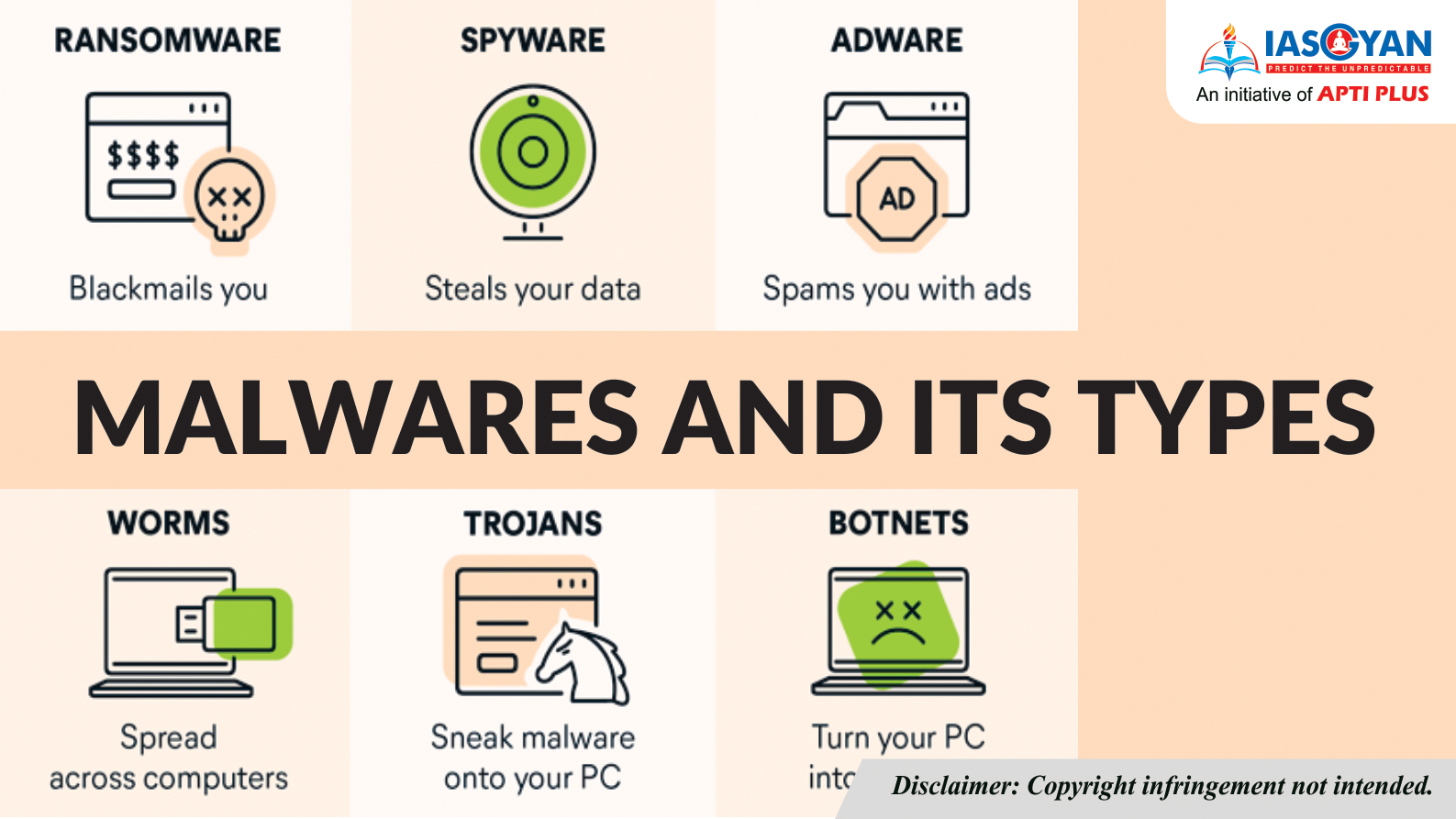
What is malware?
Malware, short for malicious software, is used by threat actors to intentionally harm and infect devices and networks. The umbrella term encompasses many subcategories, including the following:
- Viruses
- Worms
- Ransomware
- Bots
- Trojan Horses
- Keyloggers
- Rootkits
- Spyware
- Cryptomining Malware
- Adware
Malware infiltrates systems physically, via email or over the internet. Phishing, which involves email that appears legitimate but contains malicious links or attachments, is one of the most common malware attack vectors. Malware can also get onto devices and networks via infected USB drives, unpatched or fraudulent software and applications, insider threats, and vulnerable or misconfigured devices and software.
Malware can go undetected for extended periods of time. Many users are only aware of a malware attack if they receive an antimalware alert, see pop-up ads, are redirected to malicious websites, or experience slow computer speeds or frequent crashes.
Malware exploits devices to benefit threat actors. Attackers use malware to steal data and credentials, spy on users, hold devices hostage, damage files and more.

Different types of Malware
Viruses
- A computer virus infects devices and replicates itself across systems. Viruses require human intervention to propagate. Once users download the malicious code onto their devices -- often delivered via malicious advertisements or phishing emails -- the virus spreads throughout their systems. Viruses can modify computer functions and applications; copy, delete and steal data; encrypt data to perform ransom ware attacks; and carry out DDoS attacks.
- The Zeus virus, first detected in 2006, is still used by threat actors today. Attackers use it to create botnets and as a banking Trojan to steal victims' financial data. The Zeus creators released the malware's source code in 2011, enabling new threat actors to create updated, more threatening versions of the original virus.
Worms
- A computer worm self-replicates and infects other computers without human intervention. This malware inserts itself in devices via security vulnerabilities or malicious links or files. Once inside, worms look for networked devices to attack. Worms often go unnoticed by users, usually disguised as legitimate work files.
- WannaCry, also a form of ransomware, is one of the most well-known worm attacks. The malware took advantage of the Eternal Blue vulnerability in outdated versions of Windows' Server Message Block protocol. In its first year, the worm spread to 150 countries. The next year, it infected nearly 5 million devices.
Ransomware
- Ransomware encrypts files or devices and forces victims to pay a ransom in exchange for reentry. While ransomware and malware are often used synonymously, ransomware is a specific form of malware.
- There are four main types of ransomware:
- Locker ransomware completely locks users out of their devices.
- Crypto ransomware encrypts all or some files on a device.
- Double extortion ransomware encrypts and exports users' files. This way, attackers can receive payment from the ransom and/or the selling of the stolen data.
- Ransomware as a service enables affiliates, or customers, to rent ransomware. A percentage of each ransom is paid to the ransomware developer.
- Well-known ransomware variants include REvil, WannaCry and DarkSide, the strain used in the Colonial Pipeline attack.
- Data backups were long the go-to defense against ransomware -- with a proper backup, victims could restore their files from a known-good version. With the rise of extortion ware, however, organizations must follow other measures to protect their assets from ransomware, such as deploying advanced protection technologies and using antimalware with anti-ransomware features.

Bots
- A bot is a self-replicating malware that spreads itself to other devices, creating a network of bots, or a botnet. Once infected, devices perform automated tasks commanded by the attacker. Botnets are often used in DDoS attacks. They can also conduct keylogging and send phishing emails.
- Mirai is a classic example of a botnet. This malware, which launched a massive DDoS attack in 2016, continues to target IoT and other devices Research also shows botnets flourished during the COVID-19 pandemic. Infected consumer devices -- common targets of Mirai and other botnets -- used by employees for work or on the networks of employees working on company-owned devices from home enable the malware to spread to corporate systems.
Trojan horses
- A Trojan horse is malicious software that appears legitimate to users. Trojans rely on social engineering techniques to invade devices. Once inside a device, the Trojan's payload -- or malicious code -- is installed, which is responsible for facilitating the exploit. Trojans give attackers backdoor access to a device, perform keylogging, install viruses or worms, and steal data.
- Remote access Trojans (RATs) enable attackers to take control of an infected device. Once inside, attackers can use the infected device to infect other devices with the RAT and create a botnet.
- The Emotet banking Trojan was first discovered in 2014. Despite a global takedown at the beginning of 2021, Emotet has been rebuilt and continues to help threat actors steal victims' financial information.
Keyloggers
- A keylogger is a surveillance malware that monitors keystroke patterns. Threat actors use keyloggers to obtain victims' usernames and passwords and other sensitive data.
- Keyloggers can be hardware or software. Hardware keyloggers are manually installed into keyboards. After a victim uses the keyboard, the attacker must physically retrieve the device. Software keyloggers, on the other hand, do not require physical access. They are often downloaded by the victim via malicious links or downloads. Software keyloggers record keystrokes and upload the data to the attacker.
- The Agent Tesla keylogger first emerged in 2014. The spyware RAT still plagues users, with its latest versions not only logging keystrokes, but also taking screenshots of victims' devices.
- Password managers are particularly helpful in preventing keylogger attacks because users don't need to physically fill in their usernames and passwords, thus preventing them from being recorded by the keylogger.
Rootkits
- A rootkit is malicious software that enables threat actors to remotely access and control a device. Rootkits facilitate the spread of other types of malware, including ransomware, viruses and keyloggers.
- Rootkits often go undetected because, once inside a device, they can deactivate endpoint antimalware and antivirus software. Rootkits typically enter devices and systems through phishing emails and malicious attachments.
- To detect rootkit attacks, cybersecurity teams should analyze network behavior. Set alerts, for example, if a user who routinely logs on at the same time and in the same location every day suddenly logs on at a different time or location.
- The first rootkit, NT Rootkit, appeared in 1999. Hacker Defender, one of the most deployed rootkits of the 2000s, was released in 2003.
Spyware
- Spyware is malware that downloads onto a device without the user's permission. It steals users' data to sell to advertisers and external users. Spyware can track credentials and obtain bank details and other sensitive data. It infects devices through malicious apps, links, websites and email attachments. Mobile device spyware, which can be spread via Short Message Service and Multimedia Messaging Service, is particularly damaging because it tracks a user's location and has access to the device's camera and microphone. Adware, keyloggers, Trojans and mobile spyware are all forms of spyware.
- Pegasus is a mobile spyware that targets iOS and Android devices. It was first discovered in 2016, at which time it was linked to Israeli technology vendor NSO Group. Apple filed a lawsuit against the vendor in November 2021 for attacking Apple customers and products. Pegasus was also linked to the assassination of Saudi journalist Jamal Khashoggi in 2018.
Cryptomining malware
- Mining -- the process of verifying transactions within a blockchain -- is highly profitable but requires immense processing power. Miners are rewarded for each transaction they validate. Cryptojacking, the action behind cryptomining malware, enables threat actors to use an infected device's resources to conduct verification.
- Cisco found 69% of its customerswere affected by cryptomining malware in 2020, accounting for the largest category of DNS traffic to malicious sites that year.
- XMRig was the most prevalent cryptomining malwarein 2020, followed by JSEcoin, Lucifer, WannaMine and RubyMiner.
Adware
- Adware is software that displays or downloads unwanted advertisements, typically in the form of banners or pop-ups. It collects web browser history and cookies to target users with specific advertisements.
- Not all adware is malicious. Software developers use legitimate adware -- with users' consent -- to offset developer costs. Malicious adware can, however, displays ads that may lead to infection when clicked.
- Threat actors use vulnerabilities to infect systems and place malicious adware within preexisting applications. Users might also download applications already corrupted with adware. Alternately, adware can be included in a software bundle when downloading a legitimate application or come pre-installed on a device, also known as bloatware.
- Fireball, Gator, Dollar Revenue and OpenSUpdater are examples of adware.
Grayware
- The term grayware was coined in September 2004 and describes unwanted applications or files that aren't malware but worsen the performance of the computer and can cause cybersecurity risk.
- At a minimum, grayware behaves in an annoying or undesirable manner and at worst, monitors the system and phones home with information.
- Grayware alludes to adware and spyware. The good news is most antivirus software can detect potentially unwanted programs and offer to delete them.
- Adware and spyware are generally easy to remove because they are not as nefarious as other types of malware.
- The bigger concern is the mechanism the grayware used to gain access to the computer, be it social engineering, unpatched software or other vulnerabilities. Other forms of malware such as a ransomware can use the same method to gain access.
- Use the presence of adware to serve as a warning that the device or user has a weakness that should be corrected.
Malvertising
- Malvertising, is the use of advertising to spread malware. It typically involves injecting malicious or malware-laden advertisements into legitimate advertising networks and webpages.
- Advertising is a great way to spread malware because significant effort is put into ads to make them attract to users to sell or advertise a product.
- Malvertising also benefits from the reputation of the sites it is placed on, such as high-profile and reputable news websites.
Backdoor
- A backdoor is a covert method of bypassing normal authentication or encryptionin a computer, product, embedded device (e.g. router) or other part of a computer.
- Backdoors are commonly used to secure remote access to a computer or gain access to encrypted files.
- From there, it can be used to gain access to, corrupt, delete or transfer sensitive data.
- Backdoors can take the form a hidden part of a program (a trojan horse), a separate program or code in firmware and operating systems.
- Further, backdoors can be created or widely known. Many backdoors have legitimate use cases such as the manufacturer needing a way to reset user passwords.
RAM Scraper
- A RAM scraper is a type of malware that harvests the data temporarily stored in-memory or RAM.
- This type of malware often targets point-of-sale (POS) systems like cash registers because they can store unencrypted credit card numbers for a brief period of time before encrypting them then passing them to the back-end.